The Akira Ransomware Threat: An Essential Guide
Akira ransomware has rapidly become one of the most disruptive cyber threats in recent years, targeting organizations across multiple industries. According to research by CISA, between March 2023 and January 2024, the Akira ransomware group attacked over 250 organizations, demanding a total of $42 million in ransom payments.
Businesses of all sizes must understand how this ransomware operates to strengthen their defenses and minimize risk. Read this post to learn about the Akira ransomware threat, its lifecycle and practical strategies to defend against future attacks.
Understanding the Akira Ransomware Threat
Akira ransomware is a dangerous type of ransomware that employs a double extortion model. It steals sensitive data before encrypting it and threatens to leak it if the ransom is not paid. This ransomware emerged in March 2023 and supports distribution via the Ransomware as a Service model.
The number of entities that reportedly fell victim is increasing, and it includes notable organizations in different countries (especially in North America, Europe and Australia). The Akira ransomware victimslist also contains businesses operating in different industries (education, finance, manufacturing, real estate, legal, healthcare, critical infrastructure, and municipal/government services).
Akira’s typical modern ransomware campaigns are highly targeted, technically sophisticated and financially motivated. These factors combine stealthy infiltration with devastating business impact.
In addition to Windows machines, Akira is intensively focusing on attacking ESXi hosts to disrupt the operation of virtual machines and destroy them by encrypting data. This strategy makes ransomware extremely devastating and paralyzes an organization using a virtual infrastructure for business operations. Approximately 50% of attacks in 2024 targeted VMware ESXi using multiple vulnerabilities.
Initially, Akira was developed in C++, particularly the Windows version; IBM X-Force found a sample compiled in C++ in December 2023. The Akira_v2 version is written in Rust, enhancing functionality and resistance to analysis. Both Windows and Linux variants exist, tailored for respective platforms (CryptoAPI vs Crypto++).
Akira Ransomware Attack Lifecycle: Step-by-Step
To protect against Akira ransomware attacks, you should understand how this ransomware works at different stages of a cyberattack. This allows you to implement preventive measures for data protection.
Step 1 – Initial access via remote entry points
Akira ransomware actors often gain initial access through remote entry points by abusing exposed or poorly secured services. This strategy allows them to access the target network without physically touching it.
Exploitation of vulnerable VPN and RDP services
Attackers often access a victim’s network by exploiting zero-day and unpatched vulnerabilities in popular Virtual Private Network (VPN) products (gateways) and software for remote access using Remote Desktop Protocol (RDP).
Examples of the products and vulnerabilities used by Akira:
- Cisco ASA / FTD — such as CVE-2023-20269, a privilege escalation flaw in the VPN authentication process.
- SonicWall Secure Mobile Access (SMA) appliances — particularly when left unpatched or without multi-factor authentication (MFA).
- Fortinet FortiGate SSL VPN vulnerabilities — including old flaws like CVE-2018-13379, still exploited on unmaintained devices.
The tactics for unsanctioned access to a victim’s network include the following elements:
- Scan the internet for devices running outdated firmware.
- Exploit the vulnerability to bypass authentication or execute code.
- Use stolen session tokens or plaintext credentials stored in memory. Akira ransomware actors can take a mini dump of the LSASS process memory (Local Security Authority Subsystem Service) to collect additional credentials.
- Direct brute-force against weak accounts.
- Use of leaked credentials from dark web markets.
- Exploitation of RDP gateway flaws or outdated Windows Remote Desktop Services.
In some incidents, the Akira ransomware group utilized:
- AnyDesk, TeamViewer or VNC with weak or reused passwords.
- MSP RMM tools (Remote Monitoring & Management) were used when MSP accounts were compromised.
- Cloud-based admin consoles (Microsoft 365, AWS) to deploy scripts inside the network.
Note: Microsoft implemented mandatory multi-factor authentication to reduce this risk for Microsoft 365 administrators.
Compromised credentials
Attackers often use stolen credentials from previous attacks. That’s why using unique credentials and following security hygiene is important. This method allows Akira ransomware attackers to access a victim’s network without exploiting vulnerabilities. As a result, attackers appear to be legitimate users when accessing the network without compromising other security measures.
To obtain the credentials, attackers also use traditional tactics, including:
- Phishing and spear-phishing emails that capture VPN usernames and passwords.
- Keylogging/information stealers (such as RedLine Stealer) on the personal devices of remote users.
Weak spots are exploited:
- No multi-factor authentication (MFA) on VPN and email logins.
- Weak passwords that can be brute-forced.
- MFA fatigue attacks (repeated login prompts until a user accepts).
Cybercriminals can use a brute force attack if no matching credentials are found. This attack type usually targets RDP and SSH services, and it can be successful if widely known or weak passwords are used.
A typical remote-entry chain for Akira ransomware looks like this:
Internet scan → Identify exposed service → Exploit VPN or steal credentials → Authenticate to remote service → Drop recon and credential-harvesting tools → Lateral movement
Step 2 – Persistence and privilege escalation
A combination of legitimate admin tools, misconfigurations and custom scripts let Akira ransomware maintain long-term access and operate with full system rights. Persistence means staying inside the victim’s environment even after detection or reboots. After accessing the network, the attackers ensure their persistence using techniques that make their actions undetected, including creating new accounts and privilege escalation.
Creating new accounts
When infecting Windows systems, Akira ransomware adds local Windows admin users or domain admins for ongoing access. Sometimes, it disguises itself using generic names (admin, helpdesk). In Active Directory environments, Akira creates hidden accounts with delegated rights. If MFA is enabled, the attackers can sometimes steal active session tokens or cookie values from browsers to bypass re-authentication.
Configuring scheduled tasks and services
Akira ransomware creates scheduled tasks that run malicious scripts or reverse shells on startup. Then, the ransomware modifies services to launch its tools and renames malicious services to look like legitimate operating system (OS) services.
Installing remote access tools
Akira ransomware deploys AnyDesk, TeamViewer or RMM agents to retain access even if VPN credentials are revoked. It configures them to auto-start and hide from the taskbar. In Windows, registry settings are edited by modifying startup items and registry keys. Akira alters:
HKCU\Software\Microsoft\Windows\CurrentVersion\Run
and
HKLM\Software\Microsoft\Windows\CurrentVersion\Run
These techniques ensure payloads reload on reboot.
After performing these actions, Akira ransomware clears system logs to erase records that could point to its activity. These tactics make it more difficult to identify an attack. Persistence ensures Akira can return even after “cleanup” attempts, slowly exfiltrate data over time for double extortion and deploy the final ransomware payload only after getting full network control.
Privilege escalation
Privilege escalation enables Akira to transition from normal user rights to system-level or domain-level control. Akira ransomware can exploit local privilege escalation vulnerabilities by using public exploits for unpatched Windows flaws (for example, CVE-2021-34527 PrintNightmare). It also targets kernel-level vulnerabilities to gain SYSTEM privileges.
Credential dumping includes dumping Windows cached credentials, domain admin hashes and LSA secrets. Once domain admin credentials are stolen, AD can be fully controlled. Akira uses stolen NTLM hashes or Kerberos tickets to impersonate privileged users without knowing their plaintext passwords. With privilege escalation, Akira ransomware can make maximum impact when encrypting because of access to backups, shadow copies and sensitive servers, which can turn off defenses across the domain.
Step 3 – Lateral movement and reconnaissance
Akira ransomware operators perform lateral movement and reconnaissance methodically. While most ransomware uses the “fire-and-forget” approach, Akira behaves more like an advanced human-led intrusion. It can even disable some security protection software.
Once inside, the attackers aim to identify high-value data and systems, with the goal of causing further damage to the target organization. The next stage is to spread access across the network before encryption is implemented. Thus, before moving laterally, Akira needs to know what exists in the network and where the valuable targets are.
Network scanning is the first step of reconnaissance. Mapping the network enables the ransomware to identify its targets for initial attack. Built-in tools like ping, arp -a, and netstat are used to find live hosts. Other scanners, like Advanced IP Scanner or nmap, can map subnets. PowerShell scripts query Active Directory for domain structure, group memberships, organization unit (OU) hierarchy and admin account locations.
Next, Akira ransomware identifies critical assets. The targets are file servers, domain controllers, NAS devices and database servers. It looks for a backup infrastructure to disable or encrypt it later and searches for shared drives and cloud sync folders.
Akira enables remote access to services even if they are disabled:
- RDP (Remote Desktop Protocol) – often after enabling it via GPO (group policy objects) if it’s disabled.
- SMB (Server Message Block) – to copy tools and payloads across hosts.
- WMI (Windows Management Instrumentation) – to execute commands remotely without triggering RDP logs.
Akira uses stolen NTLM hashes or Kerberos tickets to authenticate on other systems without knowing the password. Dumping credentials allows disabling AV/EDR agents via stolen admin rights.
This ransomware uses legitimate tools like:
- PsExec (from Sysinternals) to run commands on remote systems.
- PowerShell Remoting to execute payloads without writing them to disk.
- Net use to mount remote shares and exfiltrate files.
Akira can utilize MSP RMM tools (ConnectWise, AnyDesk, etc.) already deployed in the environment to pivot into other machines without raising alerts. Managed service providers should be cautious and resolve MSP cybersecurity challenges to protect their own and clients’ data.
Ransomware tools and payloads are copied to other machines to prepare for the next stage of the attack.
Reconnaissance and lateral movement allow the ransomware to maximize the impact of encryption by targeting as many machines as possible simultaneously. As a result, it can access sensitive data for double extortion (data theft + encryption) and destroy backups to push the victims to pay the ransom.
Step 4 – Data exfiltration
Akira ransomware often begins by gathering and compressing sensitive data for easy transfer and obfuscation. Commonly used tools include WinRAR to compress files into archives (RAR format). Attackers may also use FileZilla, WinSCP and rclone to package and transfer stolen data. These tools are legitimate (trusted and whitelisted) and are not suspicious as specific self-made tools. In some attacks, data has been directly uploaded to MEGA cloud sharing drives configured by the attackers.
WinRAR archives have been exfiltrated using a Chrome web browser (Chrome.exe), sending compressed files to external IP ranges resembling legitimate traffic. Akira leaks data using different tools to make this process fast and effective. During one of the Akira ransomware attacks, the attackers compressed 34 GB of data with WinRAR and sent it to an external resource. After accessing the organization’s network, they took about two hours to complete the attack.
Step 5 – Encryption and operational disruption
Akira uses a hybrid encryption model. This ransomware first encrypts data with a fast symmetric cipher (ChaCha20 or KCipher-2) and then secures the symmetric key using a hardcoded RSA public key, typically RSA-4096. Each affected file has the symmetric key appended to the end and is encrypted using the embedded RSA key. Akira may partially encrypt files by blocks rather than the entire file to speed up encryption while maximizing damage. For example, small files (<2 MB) may be only 50% encrypted, while larger ones are split into multiple compressed blocks for selective encryption.
Encrypted files receive the extension “.akira” (and others like .powerranges or .akiranew in newer variants). The ransomware purposely excludes system-critical files and directories, such as .exe, .dll, system folders, Recycle Bin and Windows folders, to maintain system stability until the operation completes. Akira initiates disruption by deleting all Windows Volume Shadow Copies using PowerShell (or WMI), effectively disabling rollback options for victims.
Akira ransomware is especially aggressive against VMware ESXi hypervisors. It can encrypt entire hosts to disrupt multiple virtual machines in one attack, disable security services, halt VMs and tamper with ESXi credentials to lock out administrators.
Once the encryption is finished, Akira ransomware leaves ransom notes in each affected directory, commonly named akira_readme.txt or fn.txt. These files contain a unique victim code and a TOR-based negotiation link, threatening data release and demanding ransom in Bitcoin.
Attacking ESXi hosts
While Windows systems are the primary targets for starting the attack and spreading it over the network to infect other machines, ESXi hosts are also common targets. Let’s explore how Akira ransomware attacks ESXi hosts.
- After accessing the network, the attackers find the ESXi hosts connected to vCenter or directly accessible via SSH.
- Akira ransomware can exploit vulnerable versions of vCenter/ESXi. If patches are missing, known flaws like CVE-2021-21972, CVE-2021-21985 and CVE-2020-3992 may be abused.
- Once the attackers access ESXi via SSH (usually enabled on hosts for admin purposes), they upload and run the Akira Linux ELF encryptor directly on the host. The ransomware disables ESXi security services.
- The ransomware mounts datastore volumes on another system or uses built-in tools (vmkfstools, scp) to copy .vmdk and .vmx files to steal virtual machine data.
- Once data is stolen, Akira shuts down VMs using:
vim-cmd vmsvc/getallvms
vim-cmd vmsvc/power.off
and encrypts files on datastores using the encryptor, like in Linux.
How to Detect and Defend Against Akira Ransomware
Detection strategies are essential preventive measures that require a complex approach and should include multiple actions.
- Endpoint and network behavior monitoring. Use EDR/XDR systems (Endpoint Detection and Response/Extended Detection and Response) to detect suspicious behavior (disabling security tools, deleting shadow copies, unusual lateral movement, LSASS dumps, etc.). Also, monitor abnormal usage of file compression tools.
- Look for remote management tools (AnyDesk, RustDesk, Radmin), tunneling utilities (Ngrok, Cloudflare Tunnel) or credential theft tactics (Mimikatz, LaZagne). If you or your colleagues did not install them, it may be an early sign of a ransomware attack.
- Monitor the deployment of suspiciously signed drivers, such as rwdrv.sys (ThrottleStop), which Akira uses to load malicious drivers (hlpdrv.sys) and disable malware protection software. Akira can abuse signed drivers and these attacks are called BYOVD attacks (Bring Your Own Vulnerable Driver).
- Watch out for the mass shutdown of virtual machines. Ransomware can shut them down to start copying files and encrypting them.
- Watch out for anomalous file activity and files renamed with .akira, .akiranew or related extensions.
- Configure account and access alerts. Flag new or rediscovered “ghost” accounts created by attackers, especially if hidden from login screens.
- Detect anomalies in VPN/RDP access, such as unusual logins, failed authentication attempts or access from odd geolocations.
Together with the detection measures, you should implement defense strategies against Akira ransomware.
- Configure multi-factor authentication to access VPN, RDP, web admin tools, emails, etc. Use strong passwords and a robust security policy. Set the number of incorrect password attempts.
- Restrict external VPN/RDP access; use geo-fencing and regularly delete inactive credentials/accounts. Configure firewalls and filter network traffic. Disable unused ports.
- Regularly patch VPN appliances and systems, especially those with known Akira targets.
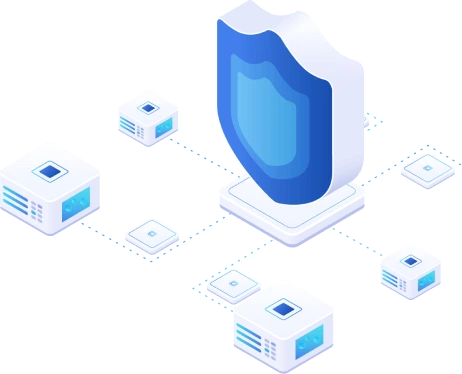
- Implement network segmentation and consider zero-trust security. Segment networks to limit the lateral movement of ransomware and prevent its spread. Use the principle of least privilege where possible to provide access only for required tasks.
- Install an antivirus (AV) with EDR/XDR software to protect computers in the network. Apply driver whitelisting to prevent execution of vulnerable signed drivers. Add protections like Moving Target Defense that block credential-dumping, lateral tools and ransomware via morphing system behavior.
Implement a reliable backup strategy that is necessary for the overall data protection strategy.
- Configure regular backups. Ensure backups are encrypted, immutable and regularly tested for recovery readiness.
- Follow the 3-2-1 backup rule. Have at least 3 copies of data, 2 stored on different media and 1 offsite. You should also have an offline, air-gapped backup that ransomware cannot access.
- Conduct regular user training: Educate users on detecting suspicious activities and what to do if unusual behavior is noticed. Users must disconnect the computer immediately if suspicious activities or signs of a ransomware infection occur and report the issue to a system administrator.
- Configure infrastructure monitoring. Monitor logs, unusual file transfers, admin account creation and strange network behavior through SIEM or third-party monitoring tools.
- Create a ransomware response plan as part of the broader disaster recovery and business continuity plans. Develop and test a ransomware-specific incident response plan, with clear roles and procedures.
Do not pay a ransom if a ransomware attack occurs. Authorities (FBI, CISA and others) advise against paying a ransom since there’s no guarantee that you will get your data back. Akira ransomware recovery presumes removing ransomware from infected computers or even reinstalling software, conducting an infrastructure audit, patching all possible vulnerabilities and restoring data from a backup.
Use NAKIVO Backup & Replication for data backup and recovery. The NAKIVO solution supports backup of physical machines, virtual machines, Amazon EC2 cloud instances, Microsoft 365 and Oracle databases (via RMAN). With a wide range of backup storage options, you can implement a reliable backup strategy. Data encryption and backup immutability protect data against unauthorized access and modification, allowing you to recover your files in case of a disaster or ransomware attack.
Conclusion
Akira ransomware remains a major cybersecurity threat, using sophisticated tactics to breach networks, encrypt data and extort victims. Understanding its lifecycle and detection methods is essential for building strong defenses and minimizing potential damage. Reliable backups, tools like NAKIVO Backup & Replication and proactive monitoring can significantly reduce the impact of an attack. By staying informed and prepared, organizations can strengthen their resilience against Akira ransomware.